[ad_1]
The elite Russian state hackers behind final 12 months’s large SolarWinds cyberespionage marketing campaign hardly eased up this 12 months, managing loads of infiltrations of U.S. and allied authorities businesses and international coverage suppose tanks with consummate craft and stealth, a number one cybersecurity agency reported.
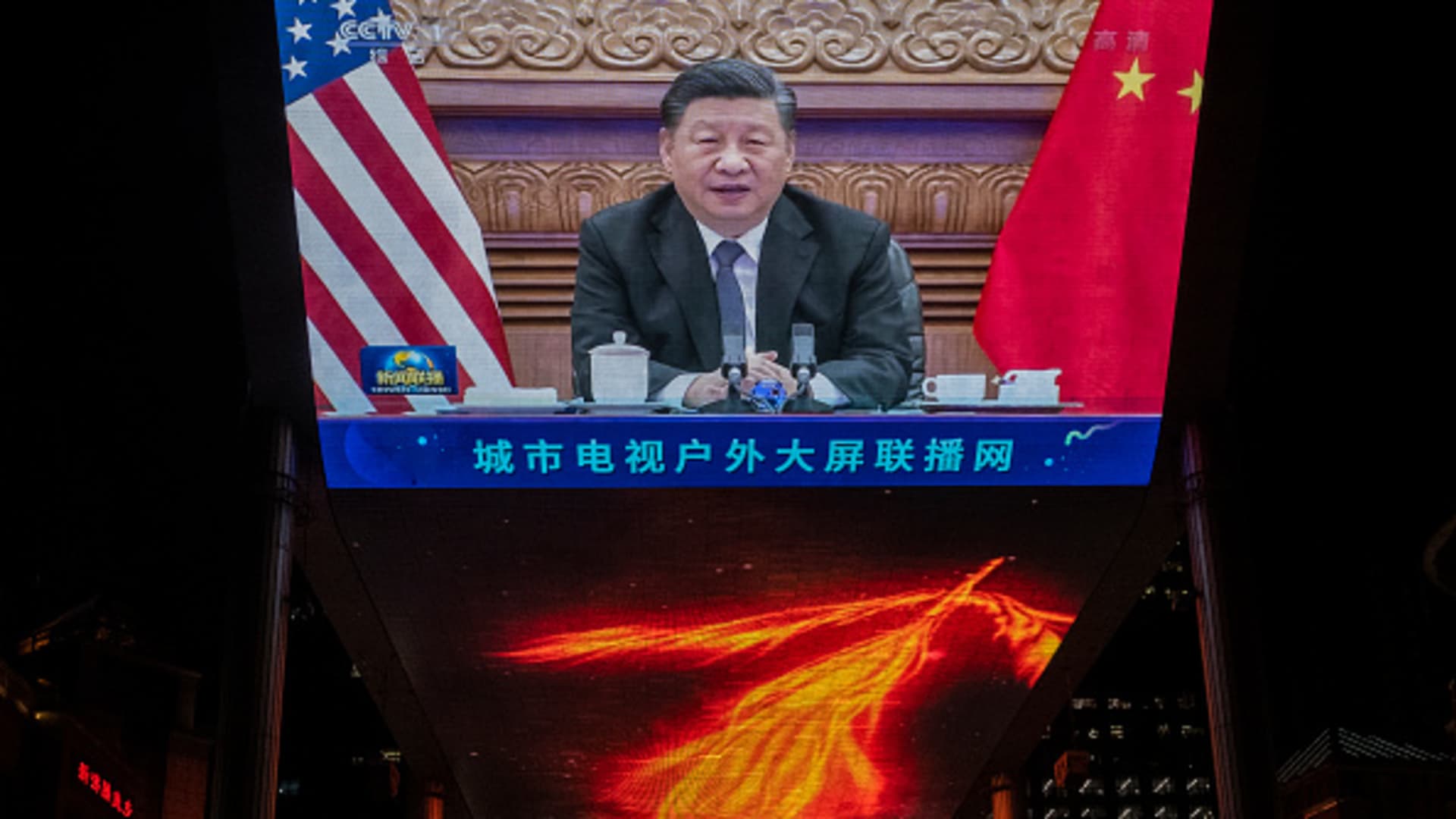
Additionally Monday, Microsoft introduced that it had disrupted the cyber-spying of a state-backed Chinese language hacking group by seizing web sites it used to assemble intelligence from international ministries, suppose tanks and human rights organizations within the U.S. and 28 different nations, the overwhelming majority in Latin America.
Microsoft stated a Virginia federal courtroom had granted its request final Thursday to grab 42 internet domains that the Chinese language hacking group, which it calls Nickel however which is also referred to as APT15 and Vixen Panda, have been utilizing to entry targets sometimes aligned with China’s geopolitical pursuits. It stated in a weblog that “a key piece of the infrastructure the group has been counting on” in its newest wave of infiltrations was eliminated.
The twin bulletins, although unrelated, spotlight the unrelenting drumbeat of digital spying by its high U.S. geopolitical rivals, whose cyber-intrusion skillset is matched solely by that of the USA.
A 12 months after it found the SolarWinds intrusions, Mandiant stated the hackers related to Russia’s SVR international intelligence company proceed to steal knowledge “related to Russian pursuits” with nice impact utilizing novel, stealthy strategies that it detailed in a principally technical report aimed toward serving to safety professionals keep alert. It was Mandiant, not the U.S. authorities, that disclosed SolarWinds.
Whereas the variety of authorities businesses and firms hacked by the SVR was smaller this 12 months than final, when some 100 organizations have been breached, assessing the injury is tough, stated Charles Carmakal, Mandiant’s chief technical officer. Total, the affect is kind of critical. “The businesses which can be getting hacked, they’re additionally dropping data.”
“Not all people is disclosing the incident(s) as a result of they don’t all the time should disclose it legally,” he stated, complicating damage-assessment.
The Russian cyber spying unfolded, as all the time, principally within the shadows because the U.S. authorities was consumed in 2021 by a separate, eminently “noisy” and headline-grabbling cyber risk — ransomware assaults launched not by nation-state hackers however slightly prison gangs. Because it occurs, these gangs are largely protected by the Kremlin.
The Mandiant findings comply with an October report from Microsoft that the hackers, whose umbrella group it calls Nobelium, proceed to infiltrate the federal government businesses, international coverage suppose tanks and different organizations targeted on Russian affairs via the cloud service firms and so-called managed providers suppliers on which they more and more rely. The Mandiant researchers stated the Russian hackers “proceed to innovate and determine new strategies and tradecraft” that lets them linger in sufferer networks, hinder detection and confuse makes an attempt to attribute hacks to them.
Mandiant didn’t determine particular person victims or describe what particular data could have been stolen however did say unspecified “diplomatic entities” that obtained malicious phishing emails have been among the many targets.
Typically, the researchers say, the hackers’ path of least resistance to their targets have been cloud-computing providers. From there, they used stolen credentials to infiltrate networks. The report describes how in a single case they gained entry to at least one sufferer’s Microsoft 365 system via a stolen session token. And, the report says, the hackers routinely relied on superior tradecraft to cowl their tracks.
One intelligent method mentioned within the report illustrates the continuing cat-and-mouse sport that digital espionage entails. Hackers arrange intrusion beachheads utilizing IP addresses, a numeric designation that identifies its location on the web, that have been bodily situated close to an account they’re making an attempt to breach — in the identical deal with block, say, because the particular person’s native web supplier. That makes it extremely tough for safety software program to detect a hacker utilizing stolen credentials posing as somebody making an attempt to entry their work account remotely.
Microsoft expressed no illusions that the web site seizures it introduced Monday would discourage the Chinese language hackers, who it has been monitoring since 2016. It stated the takedowns have been of infrastructure it has been monitoring since 2019, a lot of it exploiting on-premises —- versus cloud-based — Trade Server and SharePoint methods. The corporate has used the authorized takedown tactic in 24 lawsuits so far, Microsoft stated, knocking out a complete of 600 websites utilized by nation-state actors and 10,000 by cybercriminals.
The SolarWinds hack exploited vulnerabilities within the software program supply-chain system and went undetected for many of 2020 regardless of compromises at a broad swath of federal businesses — together with the Justice Division — and dozens of firms, primarily telecommunications and knowledge expertise suppliers and together with Mandiant and Microsoft.
The hacking marketing campaign is known as SolarWinds after the U.S. software program firm whose product was exploited within the first-stage an infection of that effort. The Biden administration imposed sanctions final April in response to the hack, together with towards six Russian firms that assist the nation’s cyber efforts.
[ad_2]
Source link