[ad_1]
President Joe Biden couldn’t have been extra blunt in regards to the dangers of cyberattacks spinning uncontrolled. “If we find yourself in a struggle, an actual taking pictures struggle with a significant energy, it’s going to be as a consequence of a cyber breach of nice consequence,” he instructed his intelligence mind belief in July.
Now tensions are hovering over Ukraine with Western officers warning in regards to the hazard of Russia launching damaging cyberattacks in opposition to Ukraine’s NATO allies. Whereas nobody is suggesting that might result in a full-blown struggle between nuclear-armed rivals, the danger of escalation is severe.
The hazard is within the uncertainty about what crosses a digital pink line. Cyberattacks, together with those who cripple crucial infrastructure with ransomware, have been on the rise for years and sometimes go unpunished. It’s unclear how grave a malicious cyber operation by a state actor must be to cross the edge to an act of struggle.
“The principles are fuzzy,” stated Max Smeets, director of the European Cyber Battle Analysis Initiative. “It’s not clear what’s allowed, what isn’t allowed.”
The USA and different NATO members have threatened crippling sanctions in opposition to Russia if it sends troops into Ukraine. Much less clear is whether or not such sanctions, whose secondary results might additionally harm Europe, could be imposed if Russia have been to significantly injury Ukrainian crucial infrastructure — energy, telecommunications, finance, railways — with cyberattacks in lieu of invading.
And if the West have been to reply harshly to Russian aggression, Moscow might retaliate in opposition to NATO nations in our on-line world with an depth and on a scale beforehand unseen. A serious cyberattack on U.S. targets would nearly definitely unleash a muscular response. However what of lesser cyberattacks? Or if Russian President Vladimir Putin restricted them to a NATO member in Europe?
Underneath Article 5 of the group’s treaty, an assault on any of its 30 members is taken into account an assault on all. However unclear is what it might take to unleash full-scale cyber retaliation. Or how dangerous an assault must be to set off retaliation from NATO’s most potent cyber army forces, led by the U.S. and Britain.
Our on-line world is exceptionally unruly. No arms management treaties exist to place guard rails on state-backed hacking, which is commonly shielded by believable deniability because it’s usually troublesome to shortly attribute cyberattacks and intelligence-gathering intrusions. The know-how is affordable and criminals can act as proxies, additional muddying attribution. Freelancers and hacktivists compound the issue.
In 2015, the main powers and others agreed on a set of 11 voluntary norms of worldwide cyber habits on the United Nations. However they’re routinely ignored. Russia helped craft them solely to knock Ukraine’s energy grid offline that winter and set in movement its hack-and-leak operation to intrude within the 2016 U.S. presidential election.
Hacking is now a core element of nice energy battle. In 2016, NATO formally designated our on-line world a “area” of battle, alongside land, sea and air.
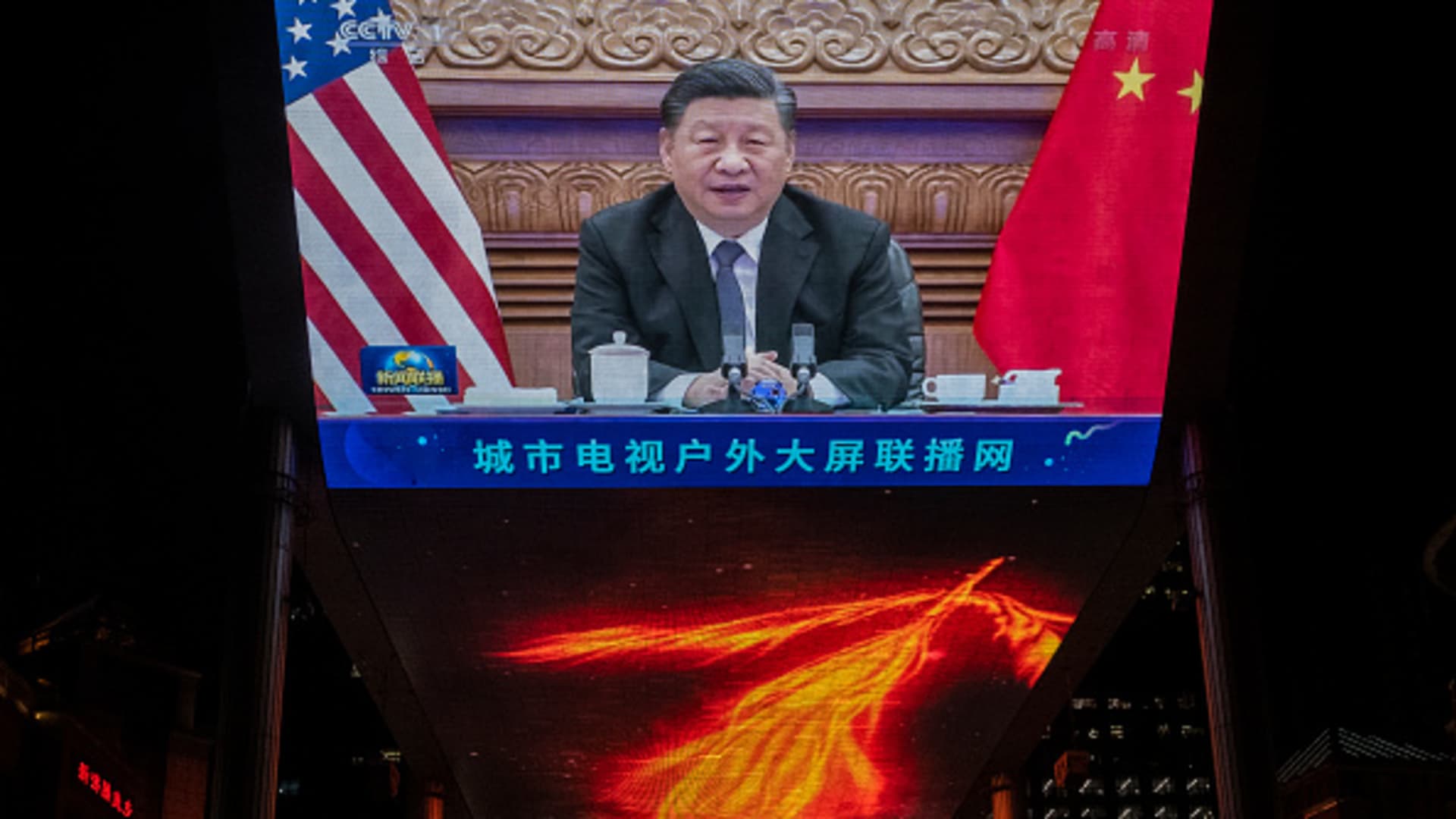
Nowhere has the militarization of our on-line world been extra clear than in Putin’s bid to return Ukraine to Moscow’s orbit.
To Serhii Demediuk, the No. 2 official on Ukraine’s Nationwide Safety and Protection Council, a loud cyberattack final month was “a part of a full-scale Russian operation directed at destabilizing the state of affairs in Ukraine, geared toward exploding our Euro-Atlantic integration and seizing energy.”
The assault broken servers on the State Emergency Service and on the Motor Transport Insurance coverage Bureau with a malicious “wiper” cloaked as ransomware. The injury proved minimal, however a message posted concurrently on dozens of defaced authorities web sites stated: “Be afraid and count on the worst.”
Such assaults are apt to proceed as Putin tries to “degrade” and “delegitimize” belief in Ukrainian establishments, the cybersecurity agency CrowdStrike stated in a weblog on Russian army cyber wreckage within the former Soviet republic: Winter assaults on the ability grid in 2015 and 2016 have been adopted by NotPetya, which exacted greater than $10 billion in injury globally.
Michele Markoff, the U.S. State Division’s deputy coordinator for cyber points, thinks “muscular diplomacy” is the one approach to finish such “immoral, unethical and destabilizing habits.”
However how? Not like nuclear arms, cyberweapons can’t simply be quantified, verified and restricted in treaties. Nor are violators apt to be held accountable within the United Nations, not with Russia and China wielding veto energy on its Safety Council.
“We’ve wallowed sort of in a quagmire for years now on making transgressors accountable,” stated Duncan Hollis, a Temple Legislation professor and former State Division authorized adviser.
Members endorsed in Might an replace to the 2015 U.N. norm s that additional delineates what must be out of bounds: together with hospitals, vitality, water and sanitation, schooling and monetary providers. That has hardly deterred Russian-speaking ransomware crooks, who’re on the very least tolerated by the Kremlin. Nor have U.S. indictments of Russian and Chinese language state hackers and the blacklisting of tech corporations accused of aiding them helped a lot.
Underneath a brand new coverage NATO adopted final 12 months after U.S lobbying, an accumulation of lower-level cyberattacks — far beneath, say, blacking out the U.S. East Coast — might be sufficient to set off Article 5. However NATO is imprecise on what a tipping level is perhaps.
NATO’s doctrinal shift adopted a pair of seismic cyberespionage shocks — the extremely focused 2020 SolarWinds provide chain hack by Russia that badly rattled Washington and the reckless March 2021 Microsoft Trade hack attributed to Chinese language state safety that set off a legal hacking free-for-all.
A cluster of wholesale information pilfering within the mid-2010s attributed to China — from the U.S. Workplace of Personnel Administration, United Airways, Marriott lodges and the well being insurer Anthem — inflicted a deep nationwide safety wound. And U.S. officers have apprehensive for greater than a decade about rivals — Russia particularly — quietly “pre-positioning” sufficient malware in U.S. crucial infrastructure together with the vitality sector to trigger appreciable chaos in an armed battle.
In response, U.S. Cyber Command developed a method in 2018 it calls “persistent engagement” to counter rivals who “function constantly beneath the edge of armed battle to weaken establishments and acquire strategic benefits.”
The goal: deny foes the prospect to breach U.S. techniques by working “throughout the interconnected battlespace, globally, as shut as doable to adversaries,” Cybercom commander Gen. Paul Nakasone wrote.
That has generally meant penetrating not simply adversaries’ networks but in addition these of allies — with out asking permission, stated Smeets, the European cyber battle analyst.
Disinformation campaigns have additionally muddied the definition of a “cyber menace.” Not do they merely embody malware like NotPetya or the the Stuxnet virus that wrecked Iranian nuclear centrifuges, an operation extensively attributed to the U.S. and Israel and found in 2010.
Throughout the 2018 U.S. midterm elections, Cybercom quickly knocked offline a key Russian disinformation mill.
Most main powers have the equal of a U.S. Cyber Command for each offense and protection.
Additionally lively are terrorists, criminals working as state proxies, begrudged freelancers and hacktivists just like the Cyber Partisans of Belarus.
Hollis compares the present messy cyber second to the early nineteenth century when U.S. and European navies have been so small they usually relied on privateers — we all know them now as pirates— for high-seas soiled work.
The U.S. and different NATO companions are, meantime, serving to Ukraine get up a separate cyber army unit, stated Demediuk, the Ukrainian safety official. Since Russia seized Crimea in 2014, NATO has intently and systematically coordinating cyber actions with Ukraine, together with joint missions, he stated.
In November, Ukraine uncovered an eight-year espionage operation by brokers of Russia’s FSB in Crimea involving greater than 5,000 tried hacks. The primary objective: to achieve management over crucial infrastructure, together with energy vegetation, heating and water provide techniques, Ukraine’s state information company stated.
This month, Microsoft stated the operation, dubbed Armageddon, persists with makes an attempt to penetrate Ukraine’s army, judiciary and legislation enforcement. Microsoft detected no injury, however that doesn’t imply Russian cyber operators haven’t gained undetected footholds.
That’s the place hackers conceal till they’re able to pounce.
___
Related Press author Yuras Karmanau in Kyiv, Ukraine, contributed to this report.
[ad_2]
Source link